A major cybersecurity alert has emerged after Microsoft issued an emergency out-of-band update to address a critical vulnerability in ASP.NET Core. The flaw, tracked as CVE-2026-40372, is considered highly severe because it allows unauthenticated attackers to compromise systems and escalate privileges to SYSTEM-level access, posing a serious risk to enterprise and web applications worldwide.
What Is CVE-2026-40372 in ASP.NET Core?
The vulnerability originates in ASP.NET Core’s Data Protection cryptographic mechanism. Due to a flaw in how HMAC validation was implemented, attackers could forge authentication cookies and bypass built-in security checks. This effectively enables threat actors to impersonate legitimate users without needing valid credentials.
How the ASP.NET Core Vulnerability Works
The issue surfaced after the release of the .NET 10.0.6 update, when developers reported decryption errors in applications. Further investigation revealed that the Data Protection API incorrectly computed—or in some cases skipped—HMAC validation.
This flaw allows attackers to inject malicious payloads that are incorrectly treated as valid by the system, leading to:
- Forged authentication cookies
- Unauthorized access to antiforgery tokens and session data
- Exposure of password reset links, API keys, and session tokens
A critical concern is that tokens generated or exploited during the vulnerability window may remain valid even after applying the patch, increasing long-term risk.
Security Risks and Impact
According to Microsoft’s advisory, attackers could exploit this vulnerability to access sensitive data, read files, and modify application data. While system availability is not directly affected, the flaw severely compromises data confidentiality and integrity, making it a high-priority security threat.
Immediate Fix: Update and Rotate Keys
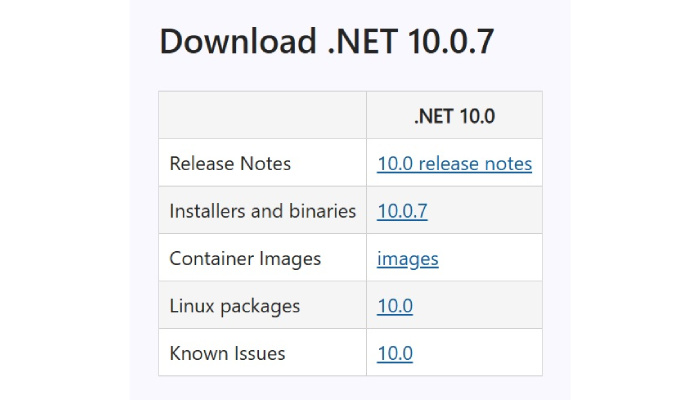
Microsoft strongly recommends upgrading the Microsoft.AspNetCore.DataProtection package to version 10.0.7 or later. However, patching alone is not sufficient. Organizations must also:
- Rotate Data Protection keys to invalidate compromised tokens
- Redeploy applications after updates
- Invalidate all authentication sessions and cookies
- Previous ASP.NET Core Security Issues
This is not the first high-severity issue affecting ASP.NET Core. A previous vulnerability (CVE-2025-55315) in the Kestrel web server allowed attackers to hijack user credentials, bypass frontend protections, and disrupt services, highlighting ongoing security challenges in modern web frameworks.
Expert Insight on Emerging Threats
Cybersecurity experts warn that modern attackers are increasingly targeting identity systems rather than traditional entry points. By exploiting authentication mechanisms, attackers can operate within trusted environments undetected, making vulnerabilities like CVE-2026-40372 particularly dangerous.
To mitigate risks and strengthen defenses, organizations using ASP.NET Core should:
- Apply the latest .NET security updates immediately
- Invalidate all session tokens and authentication cookies
- Rotate cryptographic keys regularly
- Monitor logs for suspicious or unauthorized activity
- Implement Zero Trust security models
- Enforce Multi-Factor Authentication (MFA)
- Rising Cybersecurity Threat Landscape
This incident highlights how even subtle cryptographic flaws can lead to widespread security breaches. For businesses relying on ASP.NET Core, proactive patching, continuous monitoring, and strong security practices are essential to defend against evolving cyber threats.